Client Ignoring Evidence of Targeted Spoofing Attacks
July 17, 2025
DMARC reports revealed thousands of phishing emails, yet the client continues to ignore security recommendations and enforce policies.
DMARC reports revealed thousands of phishing emails, yet the client continues to ignore security recommendations and enforce policies.
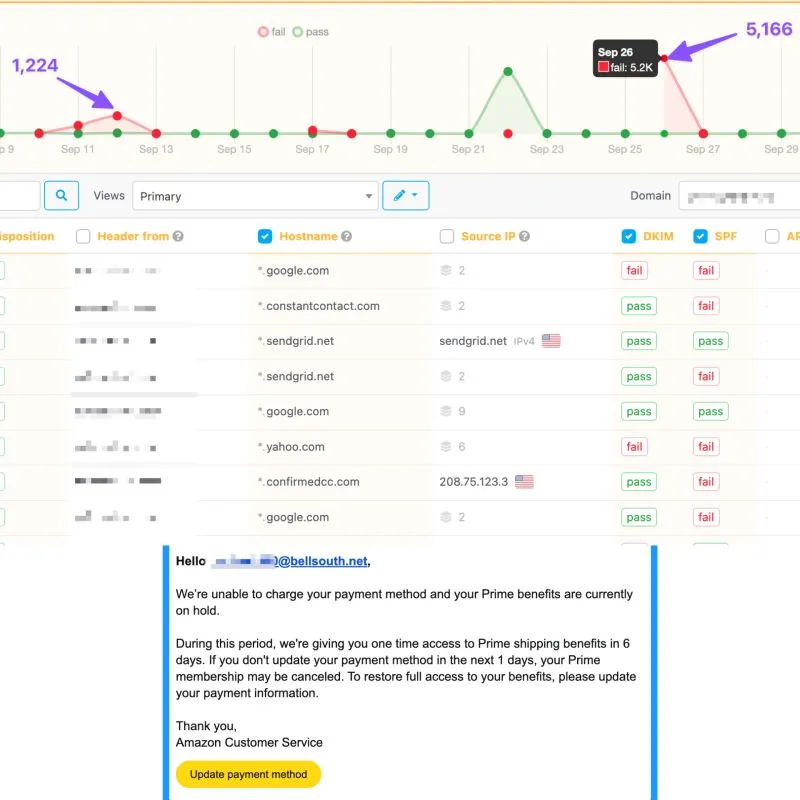
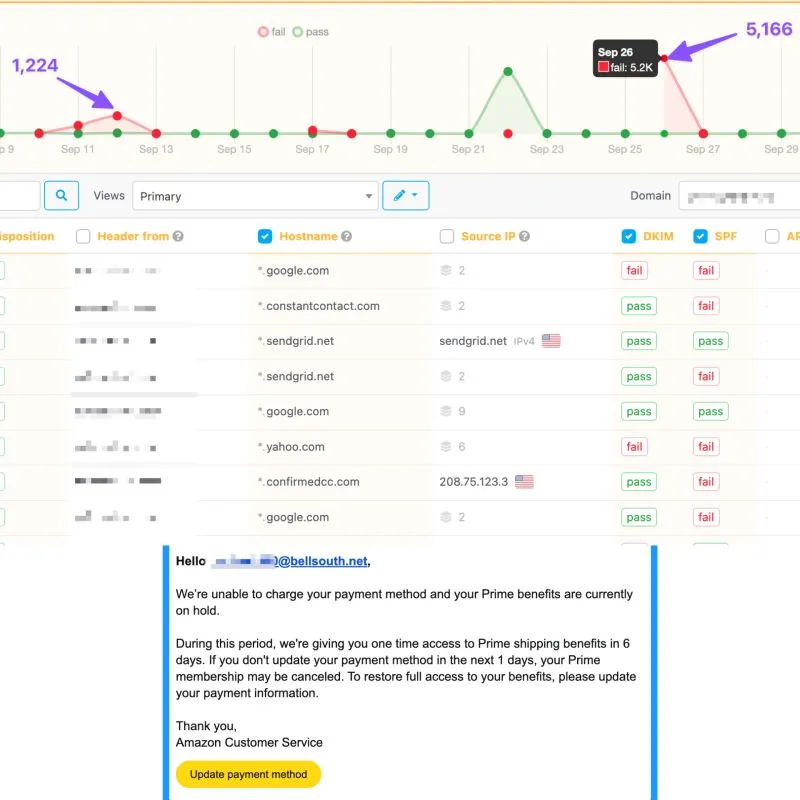
We currently have a client who is under a targeted spoofing attack. Although the client had never reported issues with fraudulent emails originating from their domain, after implementing the DMARC policy sending reports to URIports, we identified 1,224 and 5,166 phishing emails being distributed to Yahoo users through the Google infrastructure.
While the incident was reported the day after the first attack occurred and appropriate recommendations were provided, our insights were not taken seriously and were subsequently ignored.
Following the second incident, the client received several angry responses from victims, which provided further evidence of the problem. It has now been nearly a week since the incident, and the client still isn't convinced that DMARC enforcement and additional security measures are necessary.
In our experience, this is only the second case where a client ignored a spoofing issue - previously involving just a few hundred spoofed emails. This situation highlights that many business owners either don't believe or don't want to believe they can be targeted, even when clear evidence is presented.
Some of our clients even suspect that we are behind the threats, saying "We didn’t have this issue before you made changes to our DNS," despite the fact that they never had a DMARC protocol in place to begin with.
It's frustrating. How do you handle stuff like these?