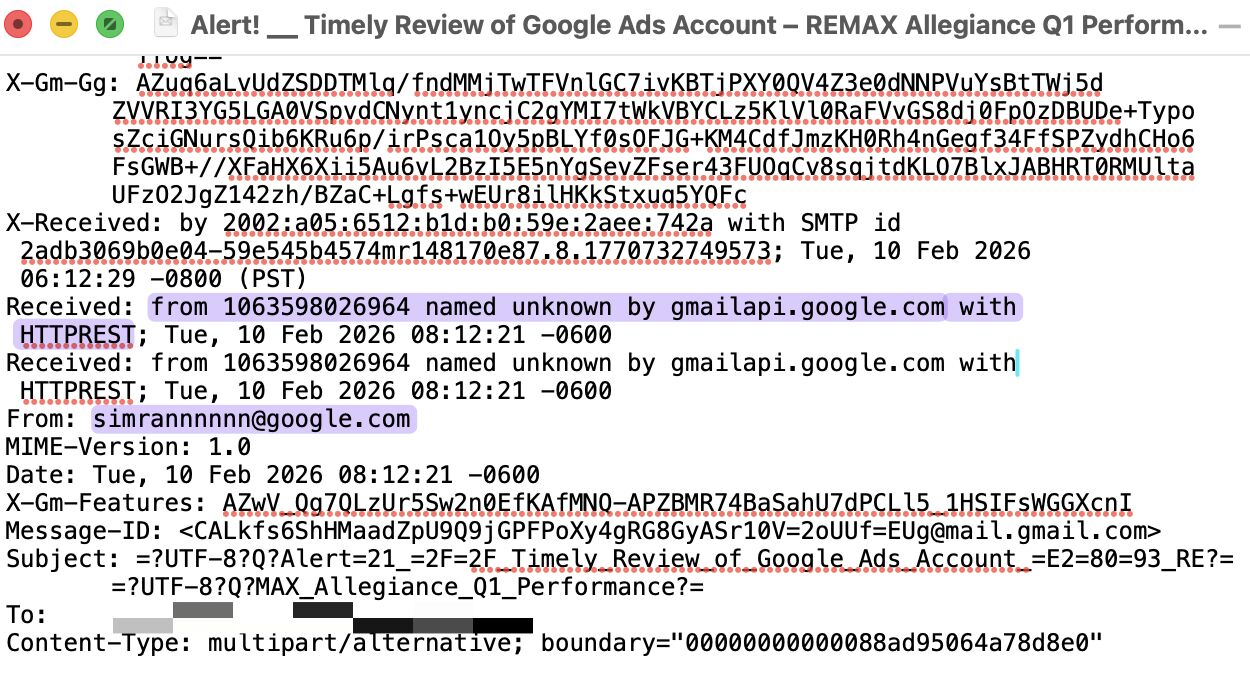
A 3rd party has deliberately blocked our ability to monitor DMARC reports for email sent from OUR domain.
DNS is managed by a marketing vendor, who claims this control is required for the website and ad to function correctly. This vendor is sending email traffic from a subdomain via Mailgun.
While DMARC for the root domain is configured and delivers aggregate reports to us, the vendor refuses to remove the DMARC configuration on the subdomain, stating that doing so would “break” their email setup.
As a result, DMARC data for our domain is being redirected to 3rd party providers without our authorization, while we are prevented from accessing visibility into the subdomain’s email performance, authentication results, and security posture.
This creates a data exposure risk, as hashtag#DMARC telemetry related to our domain is disclosed to external parties without consent. It also reduces our ability to protect the organization from domain abuse.
Revoking hashtag#DNS / NS delegation would disrupt the website, marketing, and rev-gen systems...
A good reminder to choose vendors carefully, as security risks often originate outside the organization.