Google.com Scam Sent via Gmail API - DMARC Passed, No Account Compromise
February 11, 2026
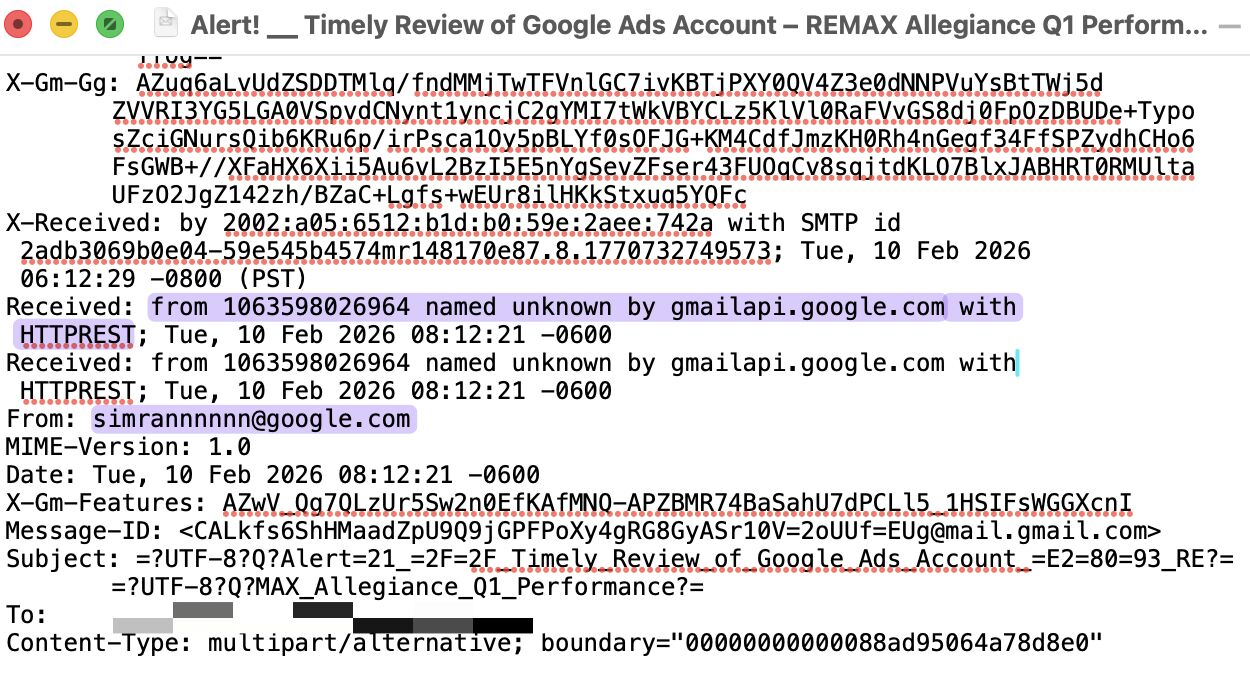
A scam email was sent from a legitimate @google.com address via the Gmail API and passed SPF, DKIM (signed by Google), and DMARC with p=reject. No account was compromised, and there were no phishing links or attachments - just social engineering designed to trigger a reply. This case shows that authentication alone cannot stop abuse when attackers operate through trusted infrastructure.