DMARC Reject Blocks Spoofing Attempt on Personal Domain
July 16, 2025
A spoofing attempt on my domain was blocked by DMARC, demonstrating the importance of DMARC, DKIM, and SPF.
A spoofing attempt on my domain was blocked by DMARC, demonstrating the importance of DMARC, DKIM, and SPF.
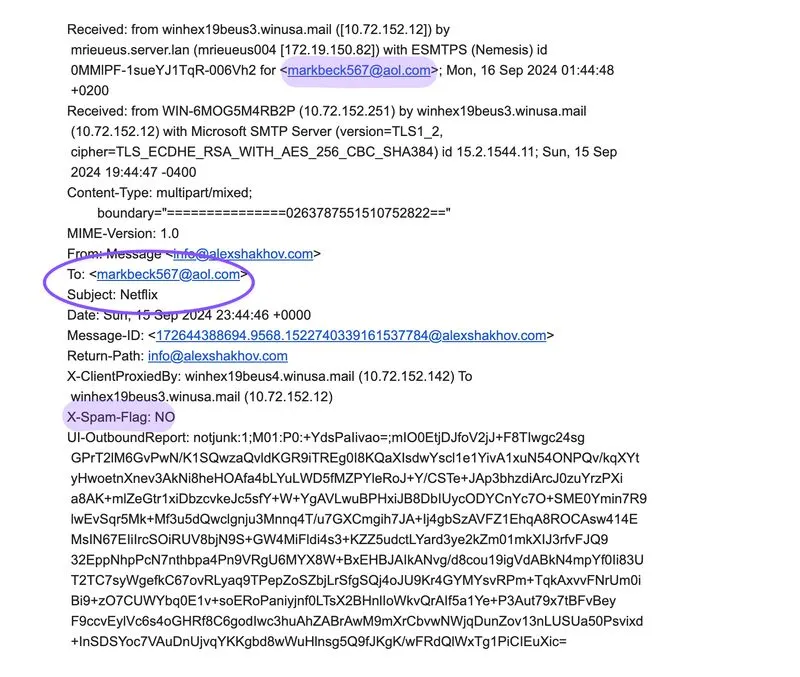
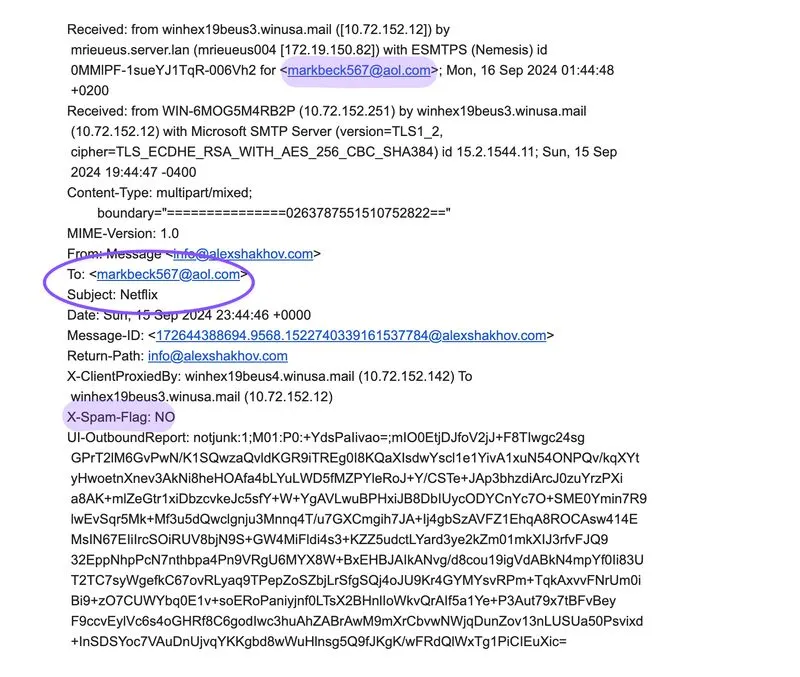
Received a spoofing attempt on my personal domain, but thanks to a strict DMARC policy set to reject, the email was blocked. Despite successfully passing Yahoo’s spam filters, it was still rejected.
The delivery error notification revealed the recipient and subject line of the attempted spoof.
DMARC, DKIM, and SPF are critical protocols to prevent TAs from impersonating legitimate individuals and businesses.