How a DMARC Misconfiguration Exposed Sensitive Email Data
November 6, 2025
Ignoring misconfigured DMARC records creates security risks, allowing threat actors to intercept sensitive data and exploit negligence.
Ignoring misconfigured DMARC records creates security risks, allowing threat actors to intercept sensitive data and exploit negligence.
My team discovered a security vulnerability in the Belgium-based hosting provider team.blue. We responsibly disclosed the issue twice through different channels, but a month later received the “out of scope / case closed” response.
During initial analysis of team.blue domain structure, we identified that one of their legacy companies, zitcom[.]dk, had a DMARC policy pointing to a non-existent domain:
rua=dmarc@dk-team[.]blue
That domain wasn’t registered, so anyone who registers dk-team[.]blue could instantly start receiving DMARC aggregate reports with sensitive data about internal infrastructure, header-to domains, sending patterns, etc.
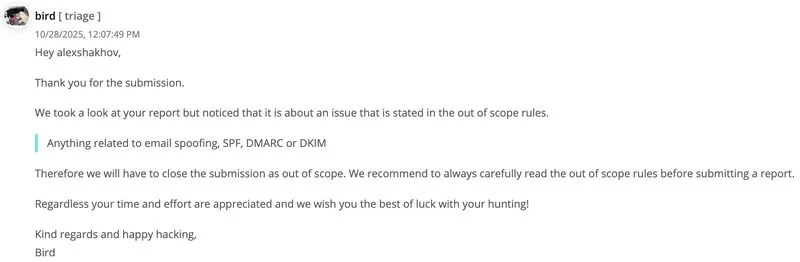
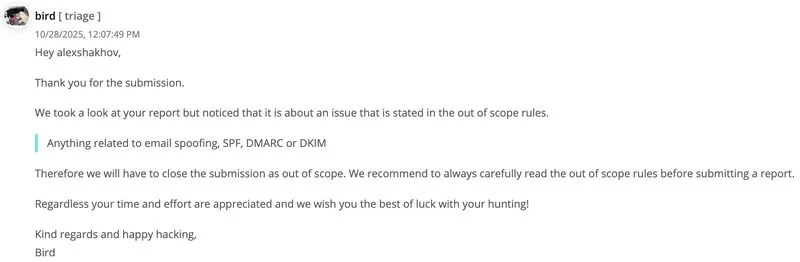
We first reported it through their Vulnerability Disclosure Policy, but they asked to re-submit it via Intigriti. The report then sat idle for two weeks before being marked as “out of scope”.
So instead of a 5 min fix in their DMARC record using the instructions provided, they chose to leave the vulnerability live.
It ended up with our team registering the domain ourselves as a protective measure to prevent its potential abuse.
And this is how threat actors exploit negligence. When organisations ignore email security, their communication data becomes vulnerable to breach.
Until cybersecurity teams and their leaders treat compromised reporting addresses as real security threats, these misconfigurations will continue to put clients, partners, and investors at risk.
Sometimes, all it takes to prevent a breach is a quick 5 min fix and someone who actually cares.