Mailchimp Auto-DKIM Can Overwrite Strict DMARC Policies
June 11, 2025
Auto-DKIM implementation by Mailchimp can overwrite p=reject DMARC, disabling protection and creating critical email security vulnerabilities.
Auto-DKIM implementation by Mailchimp can overwrite p=reject DMARC, disabling protection and creating critical email security vulnerabilities.
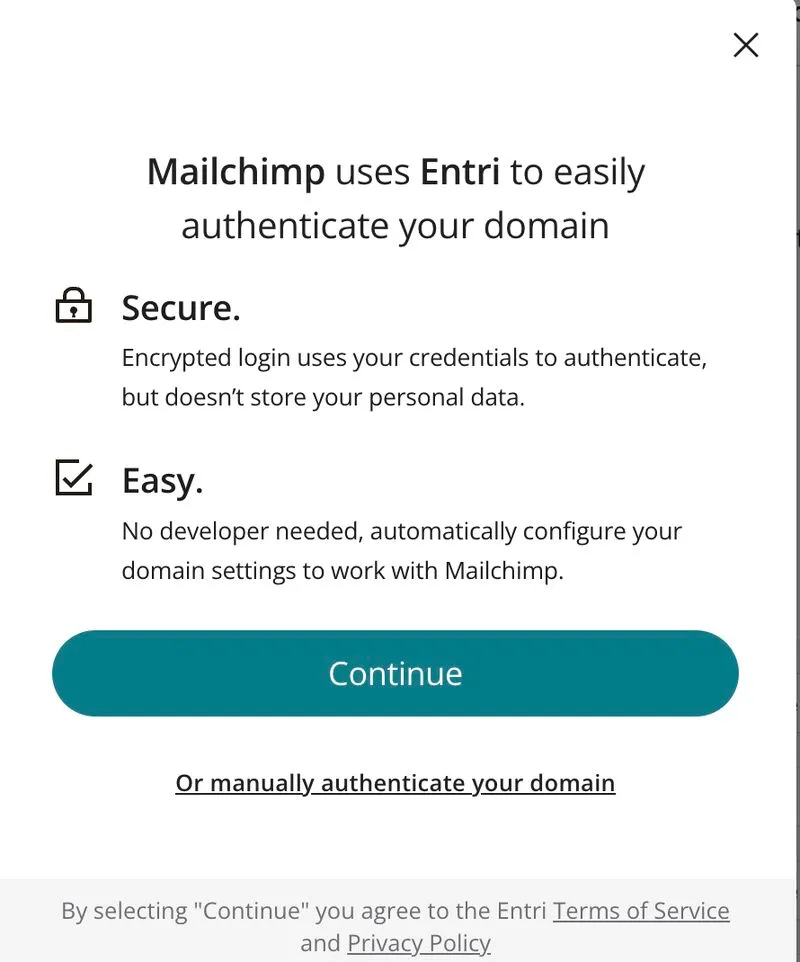
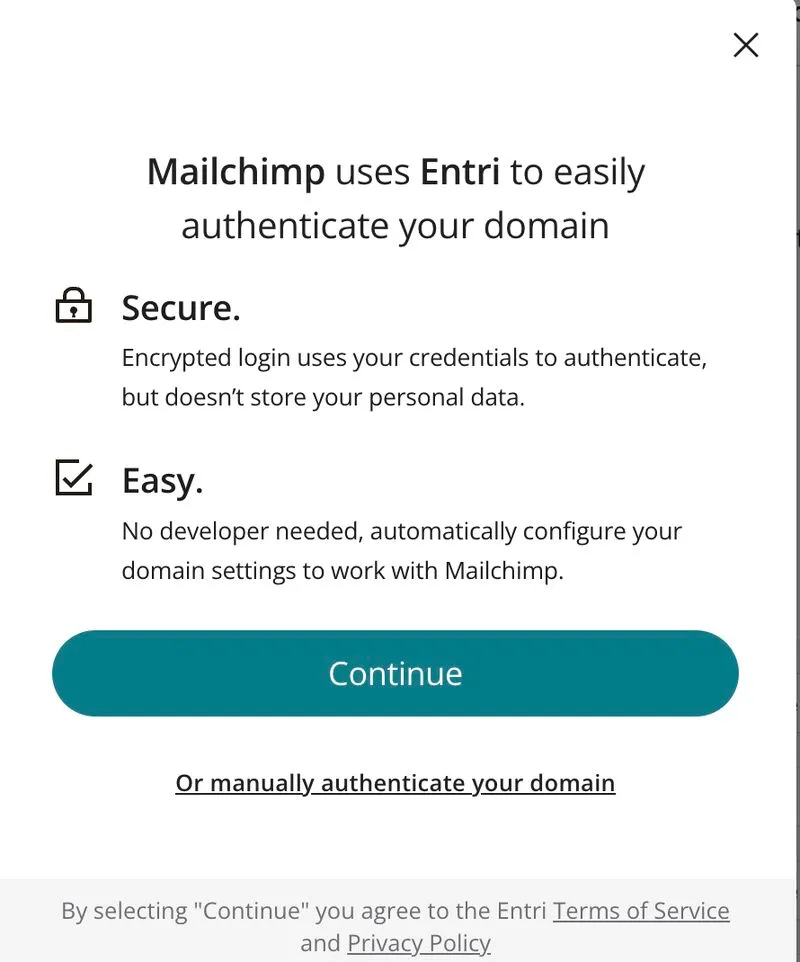
If your domain is already configured with a strict p=reject DMARC policy and you proceed with Intuit Mailchimp recommended auto-DKIM setup, Mailchimp will overwrite the existing DMARC record with a default, permissive one v=DMARC1; p=none;
And this change disables spoofing protection, leaving the domain exposed to impersonation and abuse. From a security standpoint, this creates a critical vulnerability - the domain may now be spoofed and most senders wouldn't even realize it happened.
Many users following Mailchimp’s basic setup instructions won’t check whether their DMARC policy was altered post-authentication. But the implications are serious as the removal of a p=reject policy opens the door to domain spoofing, phishing attacks, and brand abuse.
While ESPs like Mailchimp may intend to help users align with Google/Yahoo, and now Microsoft sender requirements by auto-implementing a p=none DMARC policy, replacing an existing policy without notice can compromise a domain’s overall security posture, and may lead to security issues for brands onboarding with Mailchimp.