Phishing Attacks Highlight Need for Mandatory Email Security Training
November 11, 2025
Credential harvesting attacks exploit untrained staff, emphasizing the need for regular email security exams and awareness programs.
Credential harvesting attacks exploit untrained staff, emphasizing the need for regular email security exams and awareness programs.
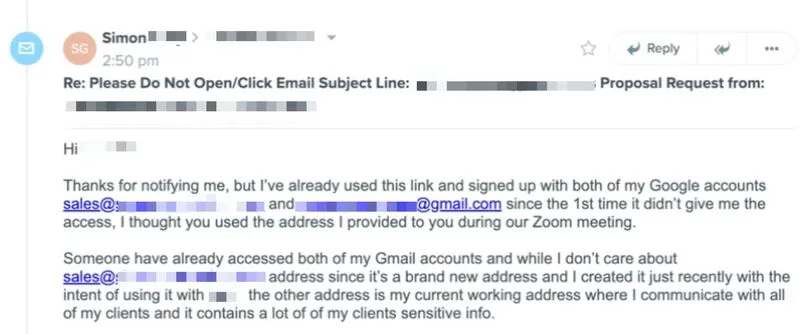
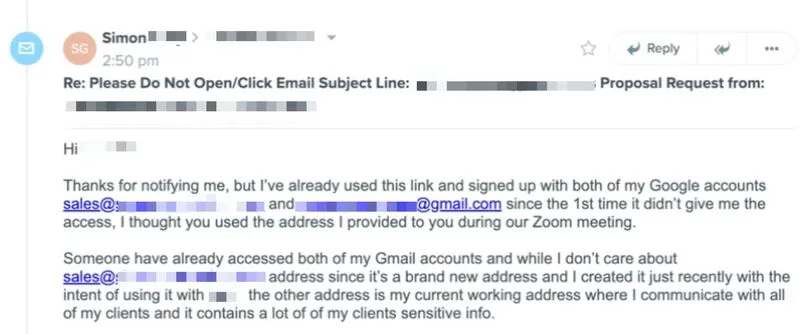
A user received a phishing link that led to a credential harvesting page. After their first login attempt failed, they attempted to sign in again, this time with a second Gmail account. As a result, both accounts were compromised.
Now, they are preparing legal action against the company whose compromised email was used to send a fully DKIM/SPF authenticated phishing email. Their company was just one of 1,800 targets across more than 1,000 orgs, reached in four batches of 450.
This is exactly what happens when employees lack training on phishing and spoofing. Even a basic URL check, verifying that the link pointed to a google[.]com domain, would have exposed the attack.
IMHO, any new hire in a role involving email should be required to pass an email security exam, much like a driver’s license test. No employee should be allowed to operate without it, and the exam should be retaken every six months to maintain vigilance.