Suspicious Google Calendar Emails Trigger DMARC Failures
May 15, 2025
New domain monitored by URIports saw unauthorized Google Calendar invites sent to Yahoo users, highlighting ongoing phishing risks.
New domain monitored by URIports saw unauthorized Google Calendar invites sent to Yahoo users, highlighting ongoing phishing risks.
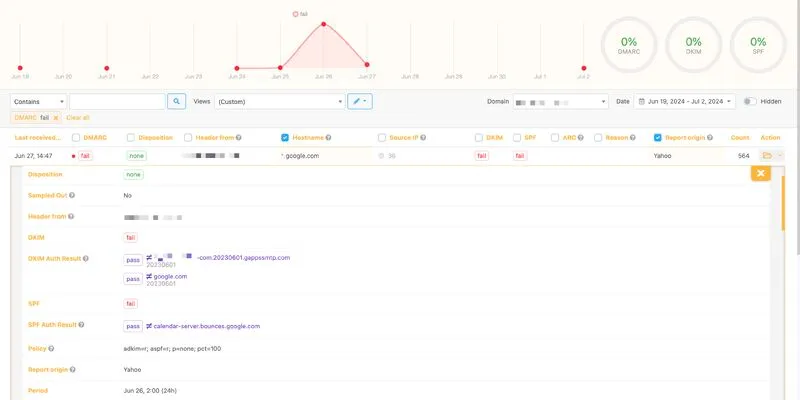
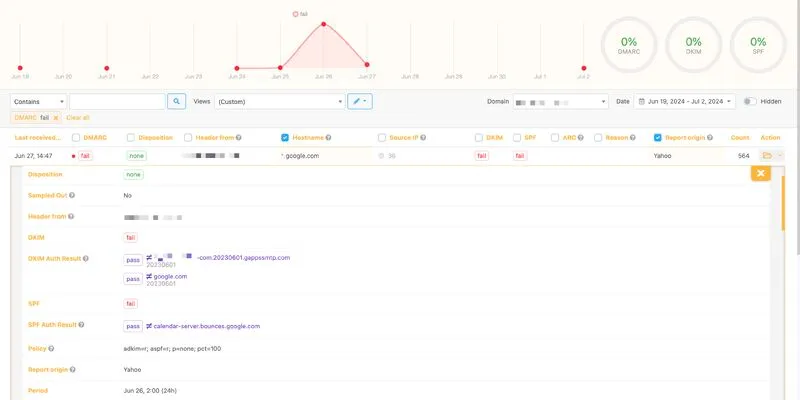
URIports alerted me that one of our monitored domains experienced increase in messages failing DMARC validation last week.
Upon reviewing the reports, I discovered traffic originating from Google servers, going through Google Calendar servers, directed towards Yahoo users.
561 Google Calendar invites were sent on June 26th alone.
This domain is relatively new to our URIports account and has been monitored for only two weeks, so we haven't enforced the policy yet. After thorough verification with the affected company's team, it was confirmed that these Google Calendar invites were not legitimate.
Despite Google having patched this exploit a few years ago, it appears there are still vulnerabilities allowing attackers to send phishing emails, particularly targeting Yahoo users, but potentially affecting others as well.
Has anyone else noticed suspicious activity related to Google Calendar recently?