The Risks of Abruptly Enforcing DMARC p=reject in Organizations
January 8, 2026
Enforcing DMARC p=reject without preparation locks legitimate emails, frustrates teams, and can cause major business disruption.
Enforcing DMARC p=reject without preparation locks legitimate emails, frustrates teams, and can cause major business disruption.
When switching to DMARC p=reject breaks organizational workflows and leads to massive churn.
Our team noticed an increased number of complaints from companies whose emails were no longer going through their CRMs.
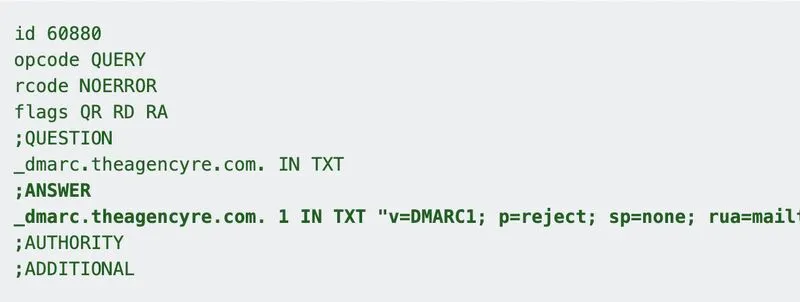
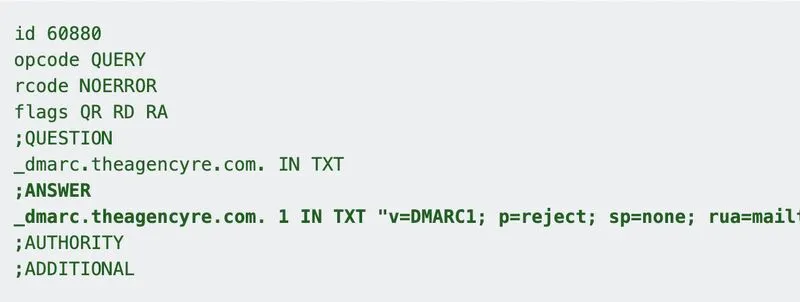
After a quick investigation, we realized these emails were being sent through the parent company’s domain - TheAGENCY, which had suddenly enforced DMARC at p=reject to reduce spoofing and impersonation.
This resulted in an immediate lockout of teams that relied on the corporate domain to send email through platforms not explicitly aligned with the HQ approved tech stack.
From a security and deliverability standpoint, it was a smart decision to prevent domain abuse.
But enforcing it abruptly and blocking millions of emails overnight left hundreds of teams under the HQ umbrella unable to operate outside of the “approved” systems.
With marketing operations deeply tied to other platforms, the sudden switch locked millions of dollars in active spend into unsupported systems.
While I fully support the decision to move to p=reject, enforcing it and blocking millions of emails overnight is not how this type of change should be communicated internally.