Why DMARC Reports Don’t Always Reveal Spoofing Activity
August 20, 2025
Even when DMARC shows no spoofing, scammers exploit blind spots, ignored policies, and unreported domains to target emails.
Even when DMARC shows no spoofing, scammers exploit blind spots, ignored policies, and unreported domains to target emails.
Threat actors love targeting business Gmail users.
That’s because Google doesn’t disclose the destination domain in DMARC aggregate reports. As a result, there’s no way to trace which companies are being phished.
At the same time, Microsoft does include the full header-to domain in its reports, which allows recipients to identify which organizations were targeted. Though it may infringe on user privacy to some extent.
Scammers are clever.
Some servers and mailbox providers don’t generate DMARC reports at all. That means anyone can send whatever they want to users of those platforms, and the activity remains invisible - no trace in any DMARC data.
Many servers also outright ignore RFC7489 and accept messages even when the domain’s DMARC policy is set to reject.
So when your DMARC reports show no spoofing activity, that doesn’t mean there are no spoofing attempts.
There almost certainly are.
Scammers are just smart enough not to leave footprints.
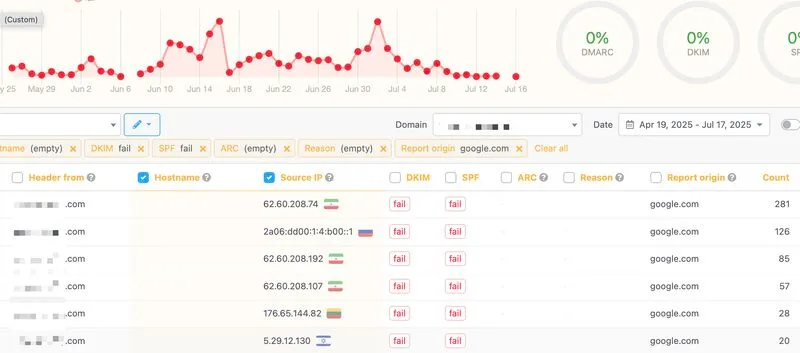
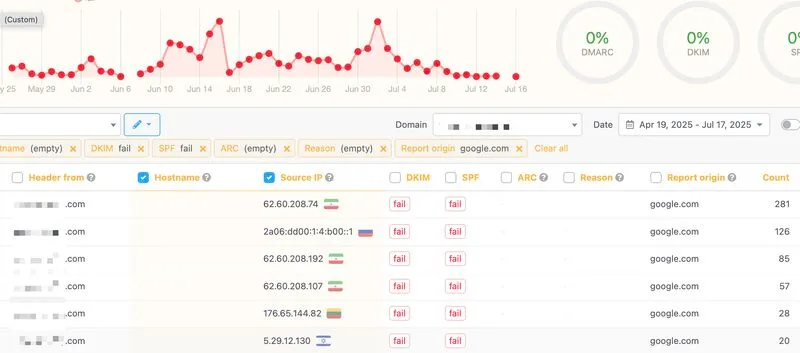
The screenshot is powered by URIports