Why Downgrading DMARC Policies Puts Brands at Risk
September 16, 2025
Allowing unauthenticated emails for CRM compatibility undermines DMARC protection, enabling ongoing spoofing campaigns and strengthening cybercriminal incentives.
Allowing unauthenticated emails for CRM compatibility undermines DMARC protection, enabling ongoing spoofing campaigns and strengthening cybercriminal incentives.
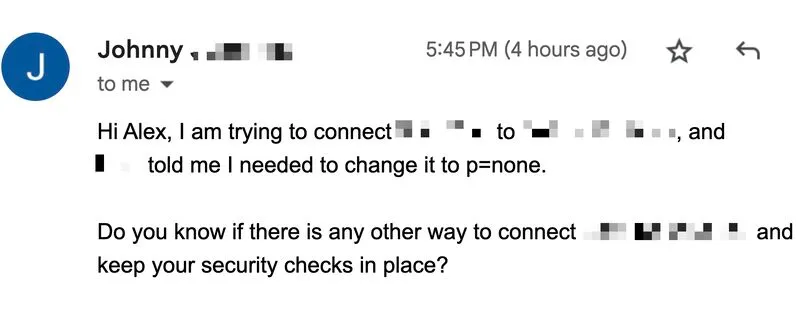
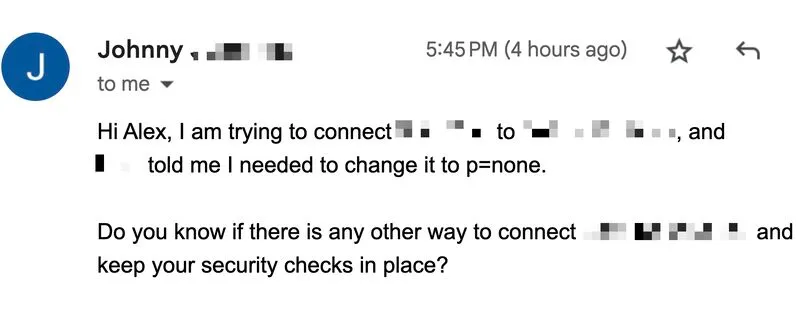
Everything you need to know about real estate - earlier today, I noticed that one of our clients, who we had worked with to set their DMARC policy to p=reject, went ahead and downgraded it to p=none with no obvious reason for doing so.
A review of their DMARC reports from the past three months confirmed the domain was still being spoofed, with hundreds of emails originating from 165.154.0.0/16, 138.183.0.0/16, 196.202.0.0/16, and others.
After I followed up directly with the company’s founder, I was told that their CRM provider had advised them to downgrade the policy to allow non-authenticated emails to pass through.
As long as technology providers see moving from p=reject to p=none as a “solution” to get emails delivered, I don’t see how email scams will become any less attractive to cybercriminals.