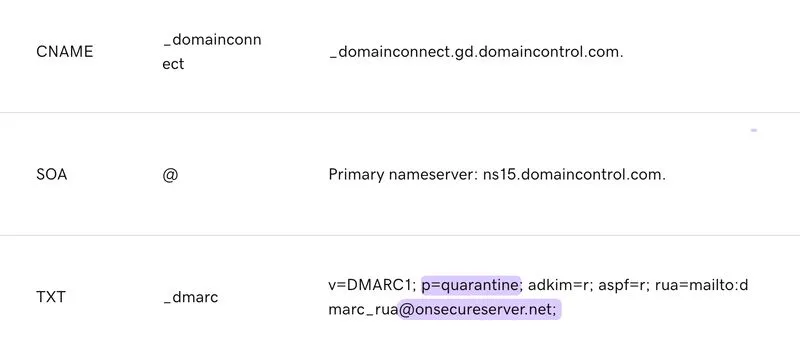
GoDaddy now enforces DMARC to p=reject/quarantine on ALL domains registered through them or using their nameservers.
While this provides instant spoofing protection, it raises serious privacy and security concerns:
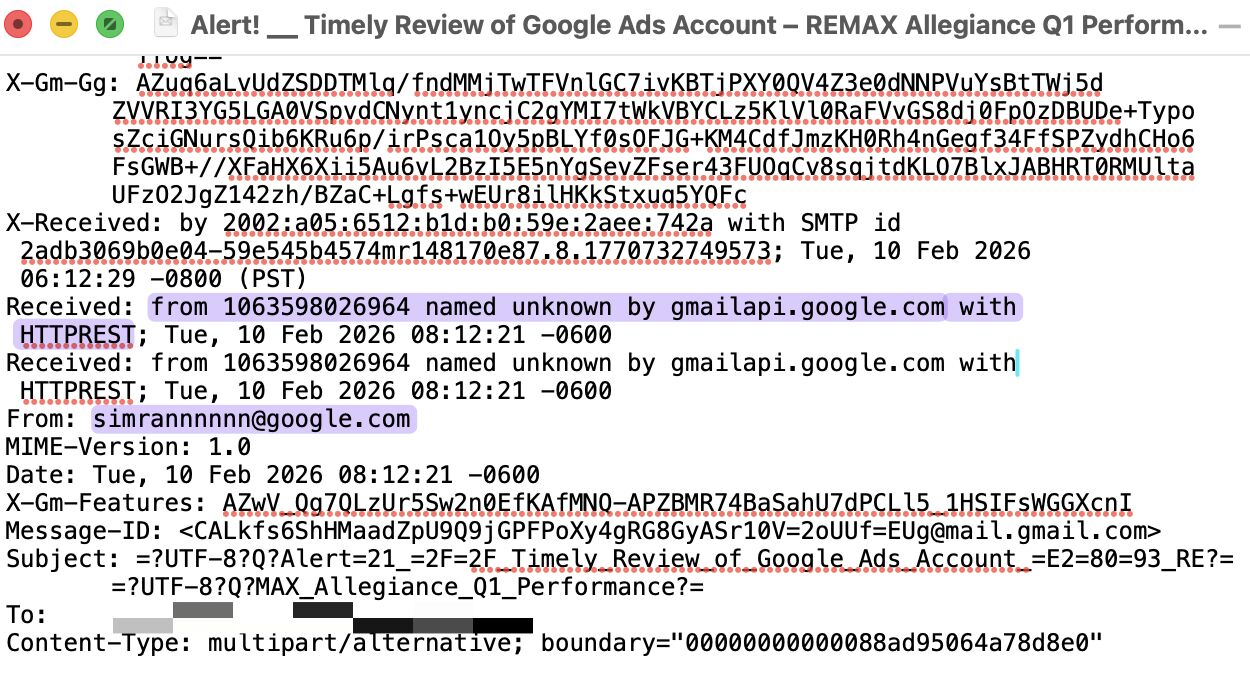
1. DMARC reports containing sending sources, IPs, authentication data, and even mail-to domains now route to a 3rd party, giving Godaddy visibility into domain owners' communications.
2. Enforcing strict policies without proper SPF/DKIM implementation breaks email delivery for millions of small businesses unfamiliar with SPF, DKIM, and DMARC (i.e. local shops, photographers, service providers, etc decided to go online)
3. Reports go to onsecureserver[.]net, registered only in mid-May 2025, with no public evidence of Godaddy ownership, potentially exposing sensitive data to unknown entities.
4. Godaddy recently shifted from p=reject default in June-July to p=quarantine default in August, showing they don't have a solid plan for this kind of enforcement.
While DMARC protection is important, I believe that enforcement decisions must remain with domain owners, not domain registrar providers.
Centralized control over email security data through 3rd-party infrastructure without explicit consent violates privacy and security principles.