Why Regular Password Changes Still Matter in Real Cybersecurity
December 18, 2025
Compromised accounts require containment; regular password changes alongside MFA remain essential to prevent escalation in real-world breaches.
Compromised accounts require containment; regular password changes alongside MFA remain essential to prevent escalation in real-world breaches.
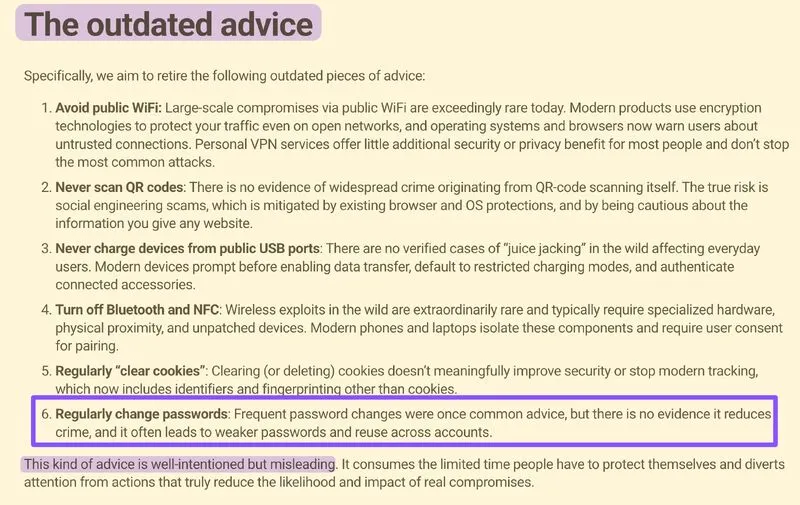
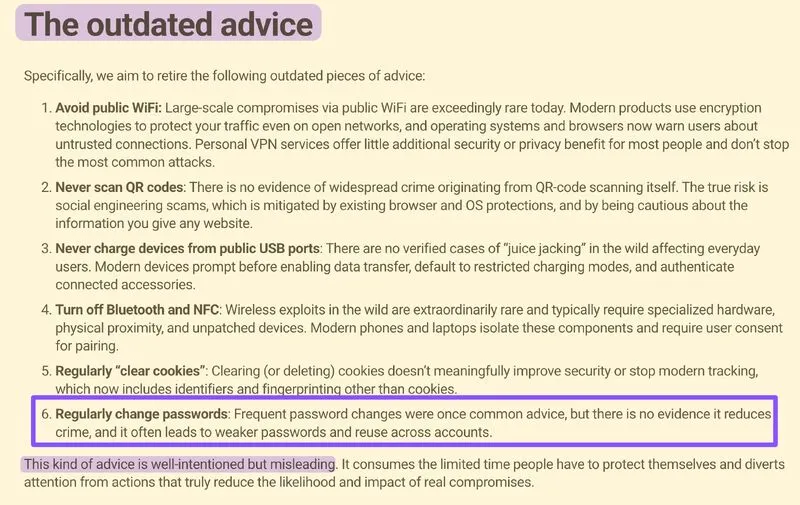
I disagree with the idea that “regularly changing passwords” is outdated advice. This came up in Hacklore, where 112 contributors collectively agreed that frequent password changes show no evidence of reducing cybercrime.
In real BEC cases, when an account is phished and credentials / session tokens are compromised, attackers often sit on that access for weeks before doing anything.
And if an organization has many users, a single compromised account often means the attacker tried to harvest others as well. In that situation, a forced organization-wide password reset is an effective containment step.
Enabling 2SV is obviously important, but it doesn’t mitigate everything. If the attacker already hijacked an active session (for example via Evilginx), then MFA offers no protection against ongoing access.
I love the Hacklore idea because it raises awareness about cybersecurity, but the current message feels a bit confusing. Security is always about tradeoffs, but that doesn’t mean we should ignore foundational best practices during real incidents.